
Google warns hackers breached Oracle apps to steal data, extort firms
A recent warning from Google indicates that corporate executives and IT teams are facing significant threats from hackers who have reportedly infiltrated Oracle Corp’s E-Business Suite, a vital component of many organizations’ operations. The extortion campaign, attributed to the notorious Cl0p ransomware group, commenced in late September and includes staggering ransom requests that could reach as high as $50 million. The hackers have alleged that they successfully breached Oracle’s software, which is integral to functions such as financial management, supply chains, and customer relations. At least one company has publicly confirmed that its systems were compromised, and several others have received alarming evidence of the breaches, including screenshots and file listings. Cybersecurity firm Halcyon, involved in addressing the situation, reported that ransom demands have surged into the millions. Cynthia Kaiser, the firm’s vice-president of ransomware research, noted, "We have seen Cl0p demand huge seven- and eight-figure ransoms in the last few days." Google's Threat Intelligence Group revealed that the extortion emails began circulating on or before September 29, utilizing hundreds of compromised third-party accounts. The attackers claimed to have extracted sensitive corporate data, employing email addresses associated with Cl0p affiliates. Halcyon experts suggested that the hackers gained access by exploiting Oracle’s default password reset procedures on public-facing portals; however, some security analysts suspect that an underlying software vulnerability may have been leveraged. Reports from those familiar with the attacks described the ransom notes as filled with spelling and grammatical errors, which aligns with patterns observed in the group’s previous operations. Victims were given contact information that parallels what is found on Cl0p’s dark web leak site, though it remains uncertain if any organizations have chosen to pay the ransom. As of now, Oracle has not issued a statement regarding these reported breaches. This incident adds to the growing list of attacks connected to Cl0p, which has previously exploited vulnerabilities in MOVEit file-transfer software, compromising data from numerous companies, including Shell and British Airways' parent company, IAG. Cl0p has gained notoriety as one of the most active ransomware groups globally, with the U.S. Cybersecurity and Infrastructure Security Agency (CISA) warning last year about their extensive reach, affecting thousands of organizations worldwide through phishing and mass email campaigns.
Market Insights: Fed Decisions, Macy's Earnings Surge, and Micron's Anticipated Growth
In today's market update, we delve into key economic indicators and corporate performances poised to shape the trading l...
CNBC | Mar 18, 2026, 12:25
Nvidia's Jensen Huang Highlights the Future of AI with Token-Based Budgets
At the recent GTC conference, Nvidia's CEO Jensen Huang emphasized a pivotal concept: AI tokens. During a dialogue with ...
Business Insider | Mar 18, 2026, 09:10Samsung and AMD Forge Alliance to Innovate AI Memory Technology
Samsung Electronics has officially partnered with Advanced Micro Devices (AMD) to advance their collaboration on cutting...
Business Today | Mar 18, 2026, 11:05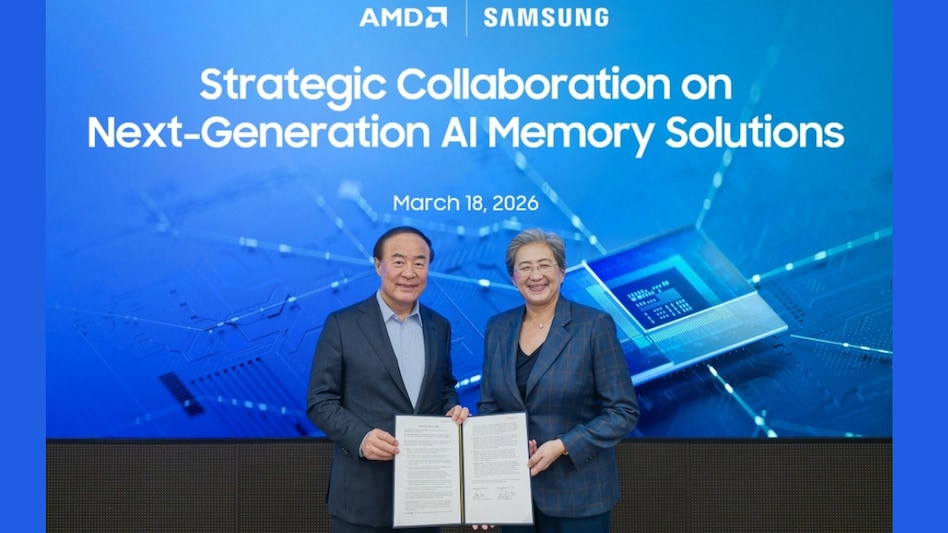
Microsoft Contemplates Legal Action Over OpenAI's AWS Partnership
Microsoft is exploring the possibility of legal action against Amazon and OpenAI regarding a proposed $50 billion partne...
Business Today | Mar 18, 2026, 08:15
Micron's Stock Surges Amid Memory Shortage as Tech Giants Struggle
Micron Technology has seen its stock price skyrocket nearly 62% in 2026, following a dramatic rise in demand for memory ...
CNBC | Mar 18, 2026, 11:45