
X is now offering me end-to-end encrypted chat. You probably shouldn’t trust it yet.
X, previously known as Twitter, has begun to introduce its latest messaging feature named "Chat" or "XChat," which is marketed as an end-to-end encrypted service. The company asserts that this feature ensures that messages can only be read by the sender and the intended recipient, leaving no access to anyone else, including X itself. However, cryptography specialists are sounding alarms about the reliability of this encryption. Concerns have arisen over XChat's implementation, which experts believe falls short of the standards set by established platforms like Signal. In XChat, users are prompted to establish a 4-digit PIN that encrypts their private key, which is then stored on X's servers. This private key, crucial for decrypting messages, is paired with a public key that enables the encryption process. A significant issue highlighted by Matthew Garrett, a security researcher, is that Signal securely keeps its users' private keys on their devices, rather than on its servers. The security of how and where X stores these keys is critical. Garrett pointed out that if X doesn't utilize specialized Hardware Security Modules (HSMs) for key storage, it could theoretically manipulate keys and decrypt messages. Although an engineer from X mentioned the usage of HSMs, there has yet to be any verification of this claim. Garrett emphasized, "Until that’s done, this is ‘trust us, bro’ territory." Another troubling aspect is acknowledged by X itself in its support documentation, which notes that the current setup could allow a malicious insider or the company to access encrypted communications. This scenario is classified as an “adversary-in-the-middle” (AITM) attack, undermining the fundamental purpose of an end-to-end encrypted messaging service. Garrett pointed out that due to how X handles public keys, it is impossible to confirm whether a new key has been generated maliciously during communication. Additionally, the implementation of XChat is not open source, in contrast to Signal's transparent documentation. X has promised to release a technical whitepaper and make its code open source later this year. Furthermore, XChat currently lacks “Perfect Forward Secrecy,” a crucial cryptographic feature that encrypts each message with a unique key, meaning that if a private key is compromised, only the last message could be decrypted, not all prior ones. This limitation has been acknowledged by the company. Experts like Garrett and Matthew Green from Johns Hopkins University continue to express skepticism. Green stated, "For the moment, until it gets a full audit by someone reputable, I would not trust this any more than I trust current unencrypted DMs." XChat, which is being rolled out alongside traditional Direct Messages, has not received responses to inquiries sent to X's press office.
Google Maps Unveils AI-Enhanced Features for a Seamless Navigation Experience
Google Maps is set to revolutionize the way users navigate their surroundings with the introduction of innovative AI-dri...
Business Today | Mar 13, 2026, 06:00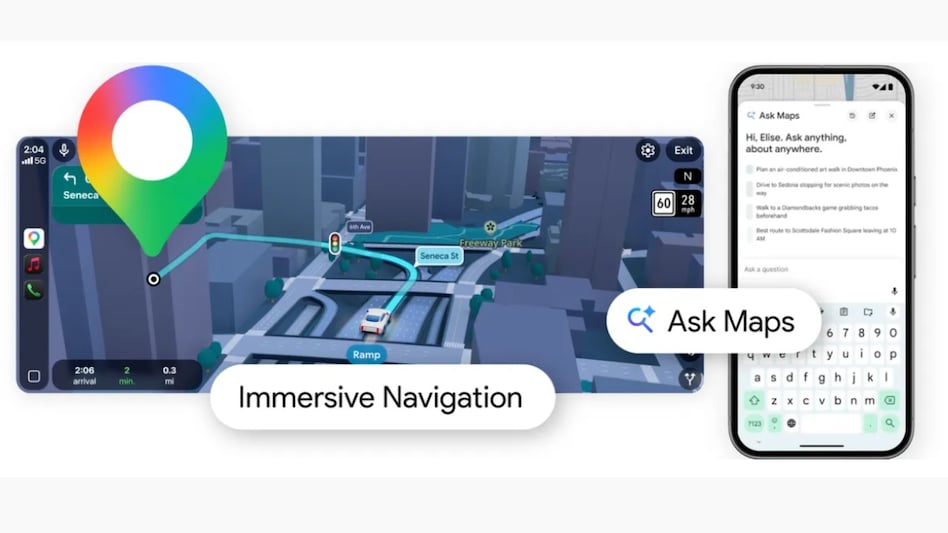
Microsoft Bids Farewell to Veteran Executive Rajesh Jha After 30 Years
Rajesh Jha, the head of Microsoft's Experiences and Devices unit, has announced his retirement after more than three dec...
Business Today | Mar 13, 2026, 05:05
Why a Startup Founder Switched from ChatGPT to Claude: A Deep Dive
In the evolving landscape of AI, many startups are reevaluating their tools. Sidhant Bendre, co-founder of Oleve, an AI-...
Business Insider | Mar 13, 2026, 09:40Elon Musk Revives Talent Search Amid xAI Leadership Exodus
In a bid to strengthen his AI startup xAI, Elon Musk has announced plans to revisit previous job applications as he face...
Business Insider | Mar 13, 2026, 08:40Adobe's Leadership Shake-Up: CEO Shantanu Narayen Steps Down Amidst AI Revolution
In a significant shift for the company, Adobe has announced that its long-serving CEO, Shantanu Narayen, will be steppin...
Business Today | Mar 13, 2026, 03:15