
Data breach reveals Catwatchful ‘stalkerware’ is spying on thousands of phones
A significant security flaw in a covert Android spyware known as Catwatchful has come to light, compromising the data of thousands of its users, including the identity of its administrator. Discovered by security researcher Eric Daigle, this vulnerability has revealed a complete database containing email addresses and plaintext passwords of more than 62,000 individuals who utilize Catwatchful to surveil the phones of their victims. Catwatchful, which presents itself as a child monitoring application, operates under the guise of being undetectable. However, it continuously uploads sensitive information from victims' devices—ranging from personal photos and messages to real-time location data—into a dashboard accessible by the installer. This spyware can also access the phone's microphone and both front and rear cameras, allowing for extensive surveillance. The term "stalkerware" is often used to describe such applications, which are typically banned from mainstream app stores and require physical access to a device for installation. The recent breach is part of a troubling trend, marking at least the fifth instance this year where consumer-grade spyware operations have leaked sensitive data. According to details from the exposed database, the majority of affected devices were located in countries such as Mexico, Colombia, India, and Peru, with some records dating back to 2018. The breach also inadvertently revealed the administrator's identity, Omar Soca Charcov, a developer based in Uruguay. Despite receiving multiple inquiries, Charcov did not respond to requests for comment. Daigle pointed out that the spyware uses a custom API that lacked authentication, making it easy for anyone online to access the entire database without credentials. Although the hosting company temporarily suspended the spyware's account, the operation soon resumed. In response to the incident, Google has implemented enhanced protections through its Google Play Protect, which now alerts users if the Catwatchful spyware is detected on their devices. However, as of the latest updates, Catwatchful continues to operate on the Firebase platform, which is under investigation for possibly violating its terms of service. The breach underscores the persistent threat posed by stalkerware, alongside the challenges faced by victims in identifying and removing such invasive applications. Resources are available for those suspecting their devices have been compromised, and it is vital for users to approach the situation with caution to avoid alerting the individuals who installed the spyware. For those in need of assistance, organizations like the National Domestic Violence Hotline and the Coalition Against Stalkerware offer critical support and resources for victims navigating these challenging circumstances.
Motorola Unveils the Game-Changing Razr Fold: A New Era in Foldable Smartphones
Motorola is gearing up to elevate its foldable smartphone lineup with the introduction of the Razr Fold, a notebook-styl...
Business Today | Jan 08, 2026, 06:45
Samsung Projects Record-Breaking Profits Amid AI-Driven Memory Chip Demand
South Korea’s Samsung Electronics is anticipating a remarkable surge in profits, projecting a threefold increase during ...
CNBC | Jan 08, 2026, 02:45
OpenAI Unveils ChatGPT Health: A New Era in Personal Health Management
OpenAI has introduced an innovative feature called ChatGPT Health, designed to assist users with health-related inquirie...
Business Today | Jan 08, 2026, 06:20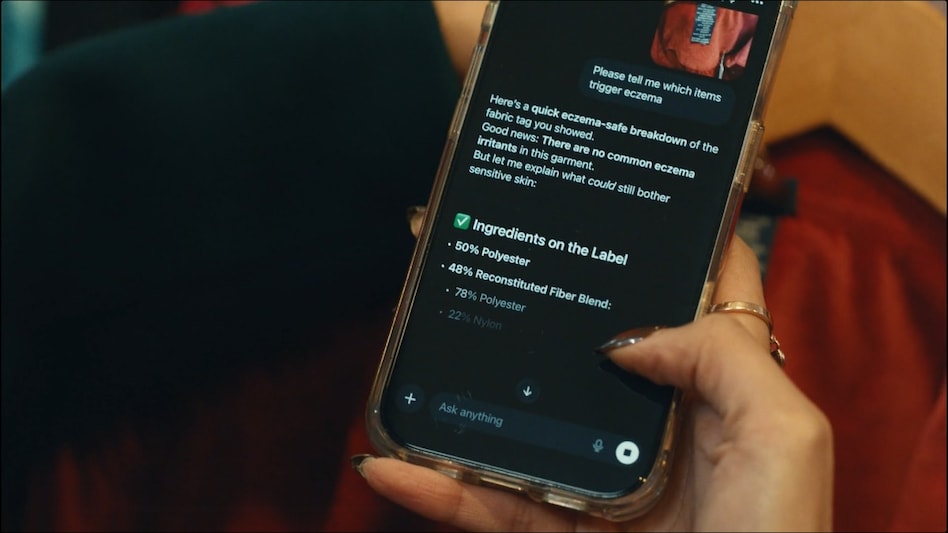
Elon Musk's Grok AI Faces Backlash Over Inappropriate Image Generation
Elon Musk's AI chatbot, Grok, has come under intense scrutiny for being inundated with sexualized images, predominantly ...
CNN | Jan 08, 2026, 09:10
Wipro Enforces Stricter Hybrid Work Policy: 6-Hour Office Requirement or Leave Deductions
Wipro, a prominent player in the IT service sector, has announced a significant update to its hybrid work policy. Accord...
Business Today | Jan 08, 2026, 05:45