
This WhatsApp scam can hijack your account without OTPs. What users need to know
A new and sophisticated scam targeting WhatsApp users has come to light, utilizing the app’s device-linking feature to gain unauthorized access to victims' accounts. Cybersecurity experts have raised alarms about this campaign, known as GhostPairing, which enables attackers to take control of accounts without needing passwords, SIM cards, or verification codes. Unlike traditional hacking methods, GhostPairing relies heavily on social engineering tactics, deceiving users into approving a malicious device themselves. This technique is reportedly difficult to detect and spreads rapidly through trusted contacts, prompting serious concerns regarding the design and understanding of device-pairing features. According to findings from the cybersecurity firm Gen Digital, the scam begins with an innocent-looking message from a trusted friend, such as "Hey, I just found your photo!" This message includes a link that appears as a Facebook-style preview within WhatsApp. By clicking the link, users are directed to a counterfeit webpage resembling a Facebook photo viewer, which prompts them to "verify" their identity before accessing the content. Unbeknownst to the user, this action activates WhatsApp’s official device-pairing process. They are then prompted to enter their phone number, which generates a numeric pairing code. The deceptive page instructs users to enter this code back in WhatsApp, presenting it as a routine security measure. By doing so, victims inadvertently authorize the attacker's device, granting them complete access to WhatsApp Web. With this access, hackers can read messages, download media, send messages as if they were the victim, and receive new messages in real time, all while the victim's phone remains unaffected and functioning normally. This makes the breach extremely challenging to detect. The campaign was first noted in Czechia, but experts warn it has the potential to spread globally. Compromised accounts are often used to propagate the same misleading links to friends and group chats, taking advantage of existing trust networks instead of relying on mass spam techniques. Researchers have pointed out that GhostPairing does not bypass encryption or exploit software vulnerabilities; rather, it capitalizes on legitimate features functioning as intended, making the situation particularly concerning. Linked devices stay active until the user manually removes them, leaving compromised accounts vulnerable indefinitely. To safeguard against GhostPairing, users are encouraged to exercise caution, as scams like this prey on human trust instead of technical weaknesses.
Apple Lowers App Store Commission in China, Strengthening Market Ties
In a strategic move to enhance its relationship with the Chinese market, Apple has announced a reduction in its App Stor...
TechCrunch | Mar 13, 2026, 15:35
Peacock Unveils Innovative AI Features and Mobile Gaming to Engage Users
Peacock is positioning itself at the forefront of entertainment by integrating artificial intelligence and mobile-centri...
TechCrunch | Mar 13, 2026, 14:25
Vaccination Rates Soar in New Mexico Amid Measles Outbreak
In January 2025, a measles outbreak emerged on the outskirts of Texas, quickly spreading to New Mexico and other neighbo...
Ars Technica | Mar 13, 2026, 15:45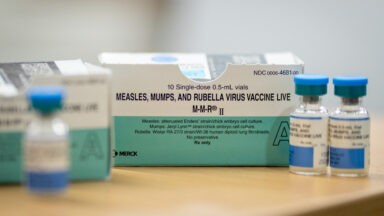
Nvidia Poised to Launch Revolutionary AI Chip in Ambitious $20 Billion Investment
Nvidia is gearing up for a major announcement regarding a groundbreaking AI chip, a venture that represents a staggering...
CNBC | Mar 13, 2026, 17:05
Amazon Ups the Ante on Prime Video: New Pricing and Features Unveiled
Beginning April 10, Amazon Prime members will see an increase in the cost of ad-free Prime Video, escalating from $3 to ...
Ars Technica | Mar 13, 2026, 17:20